The Benefits of a Water Softener for Health and Home in Denver
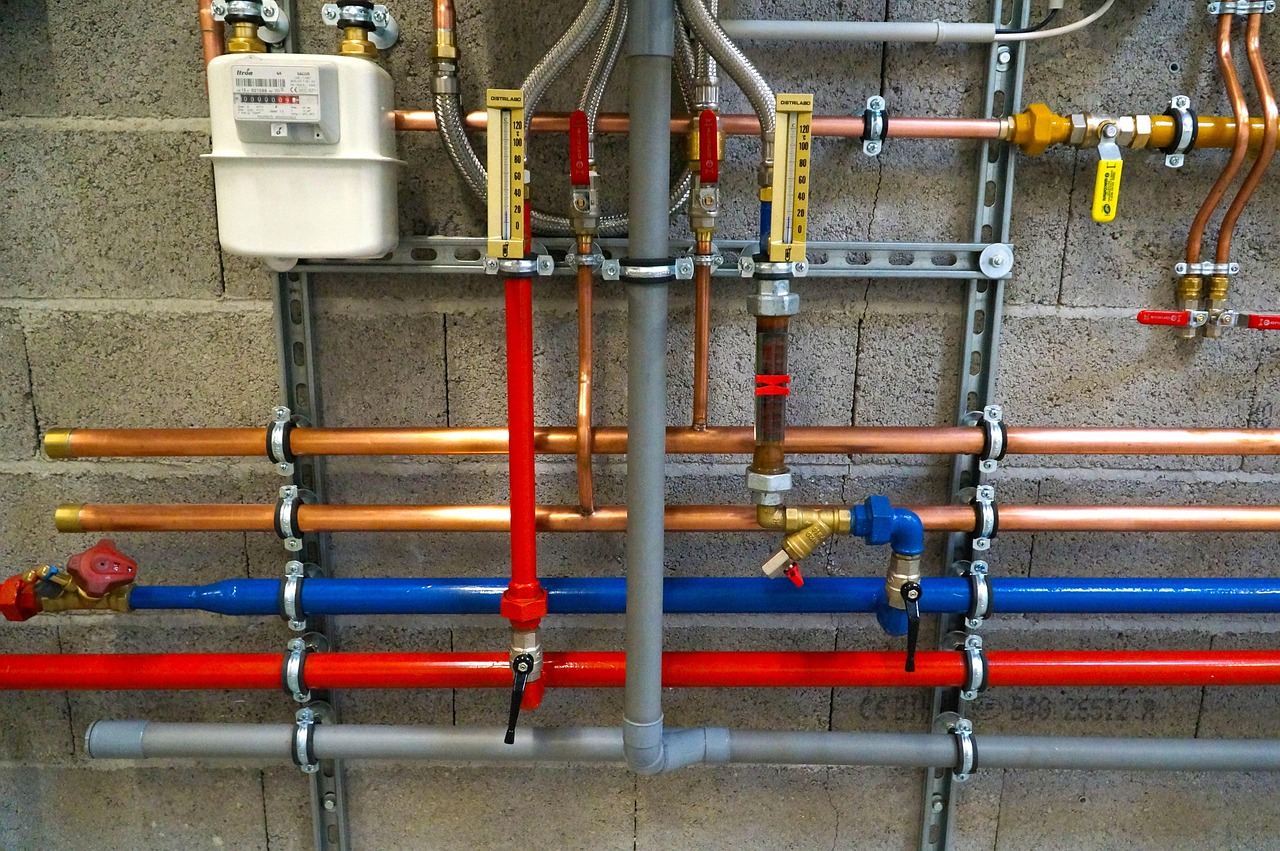
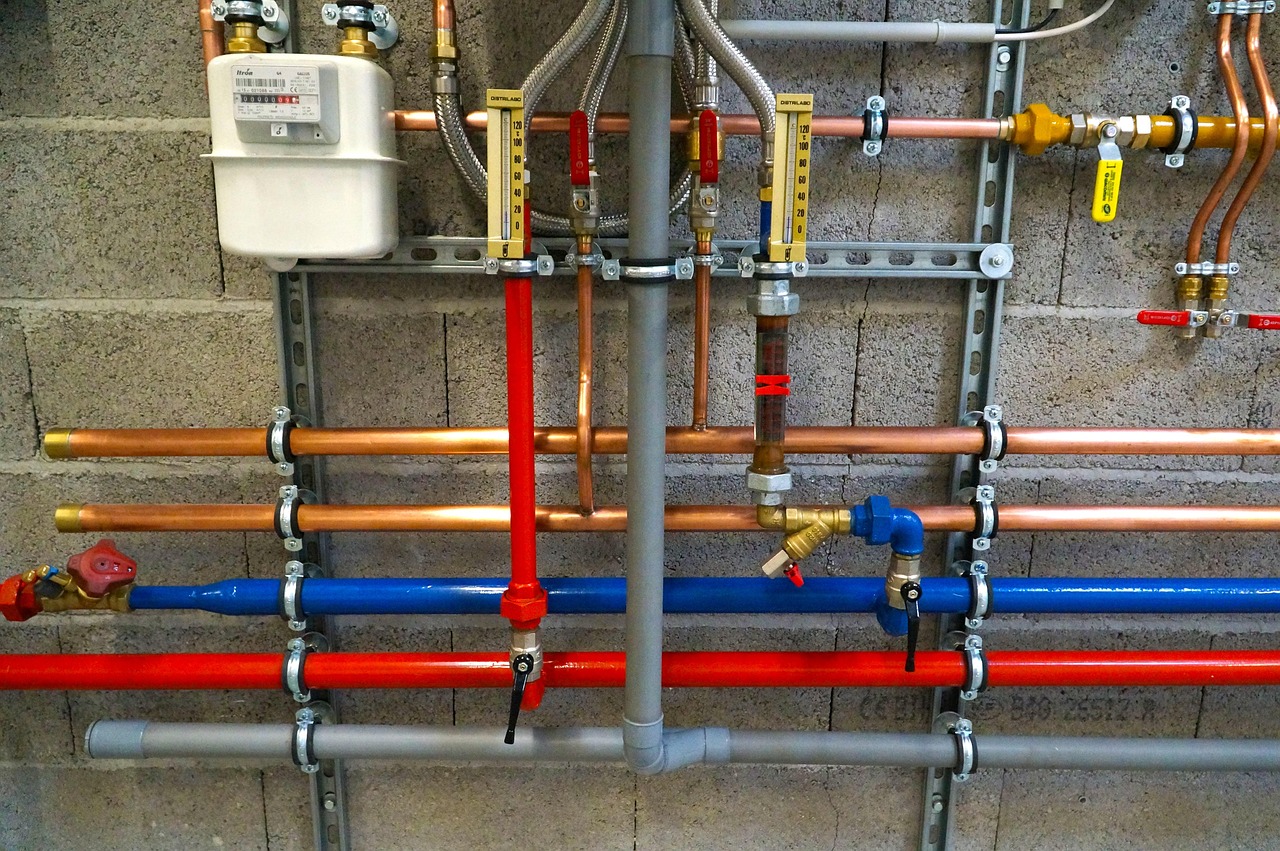
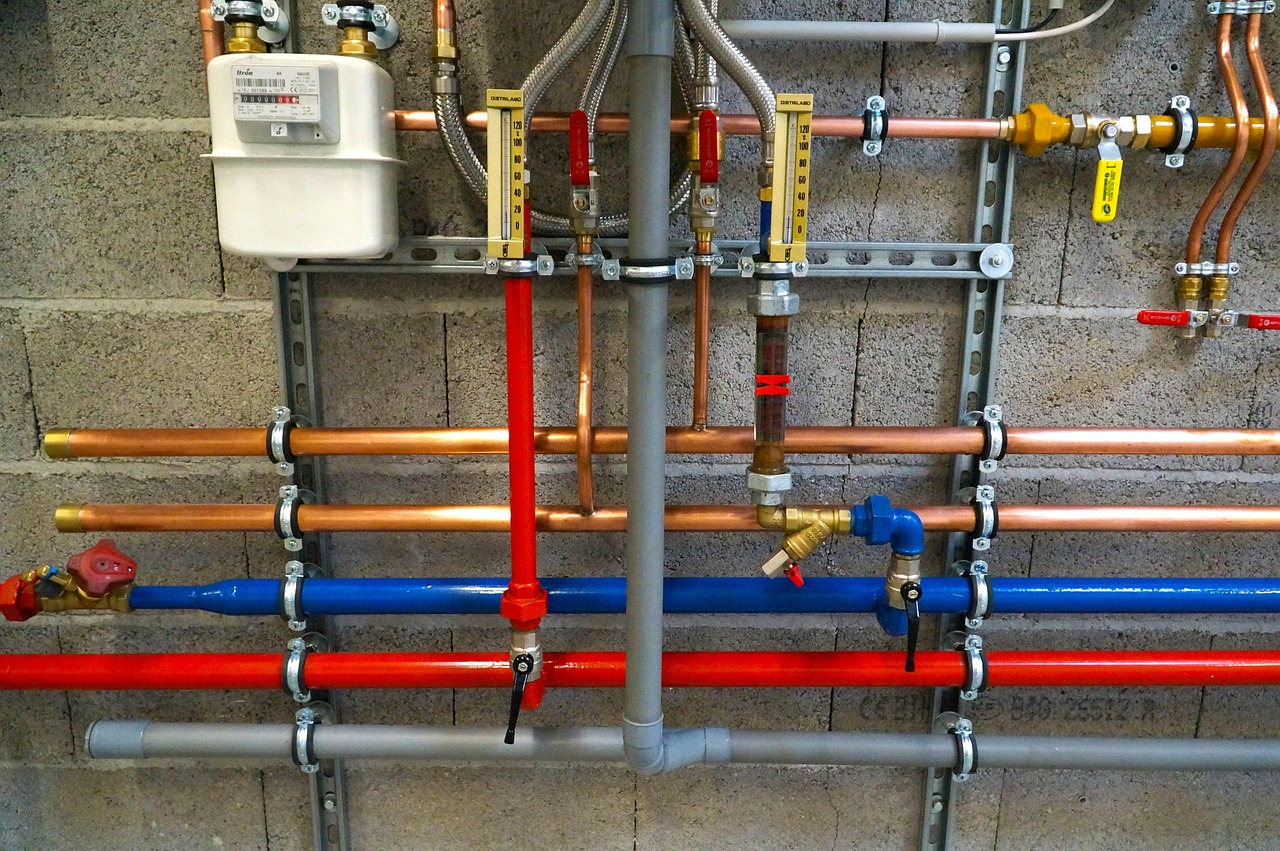
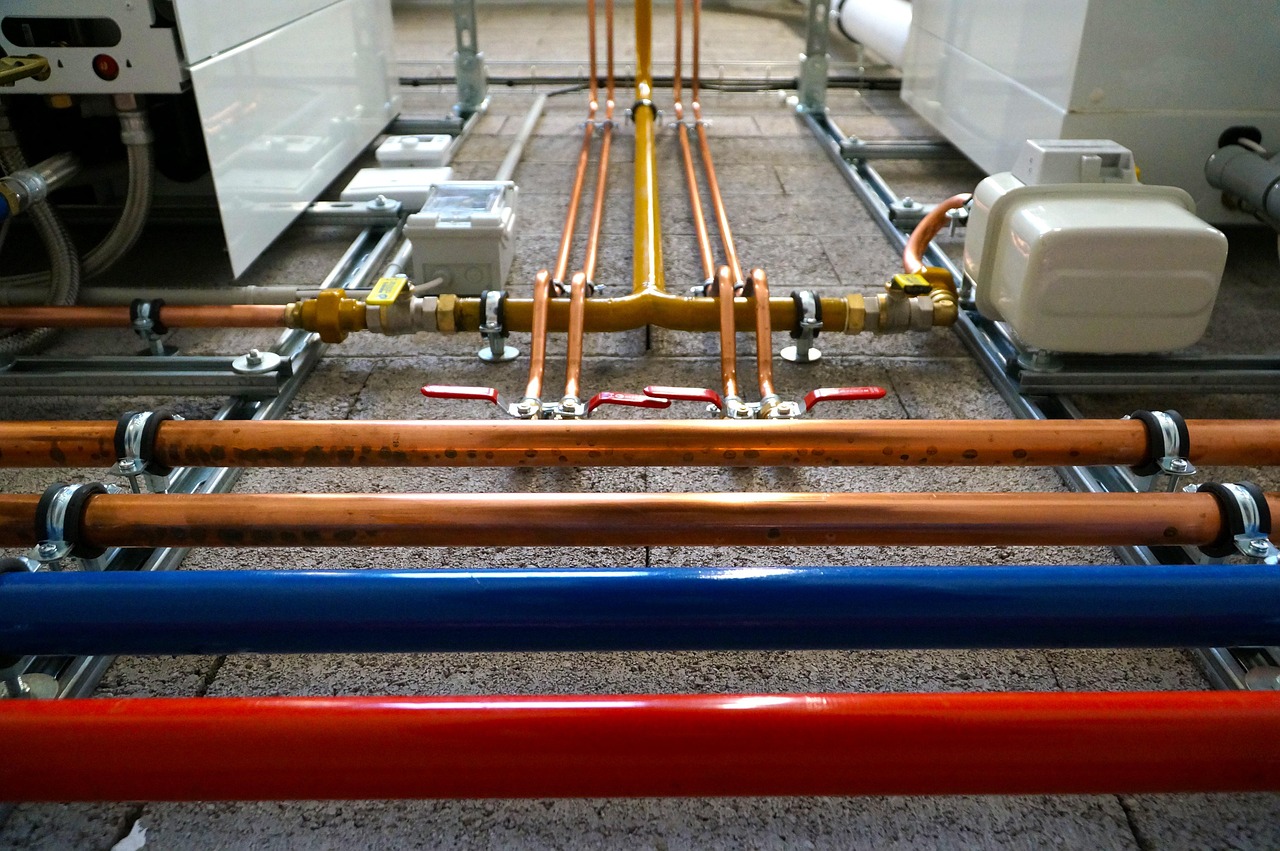
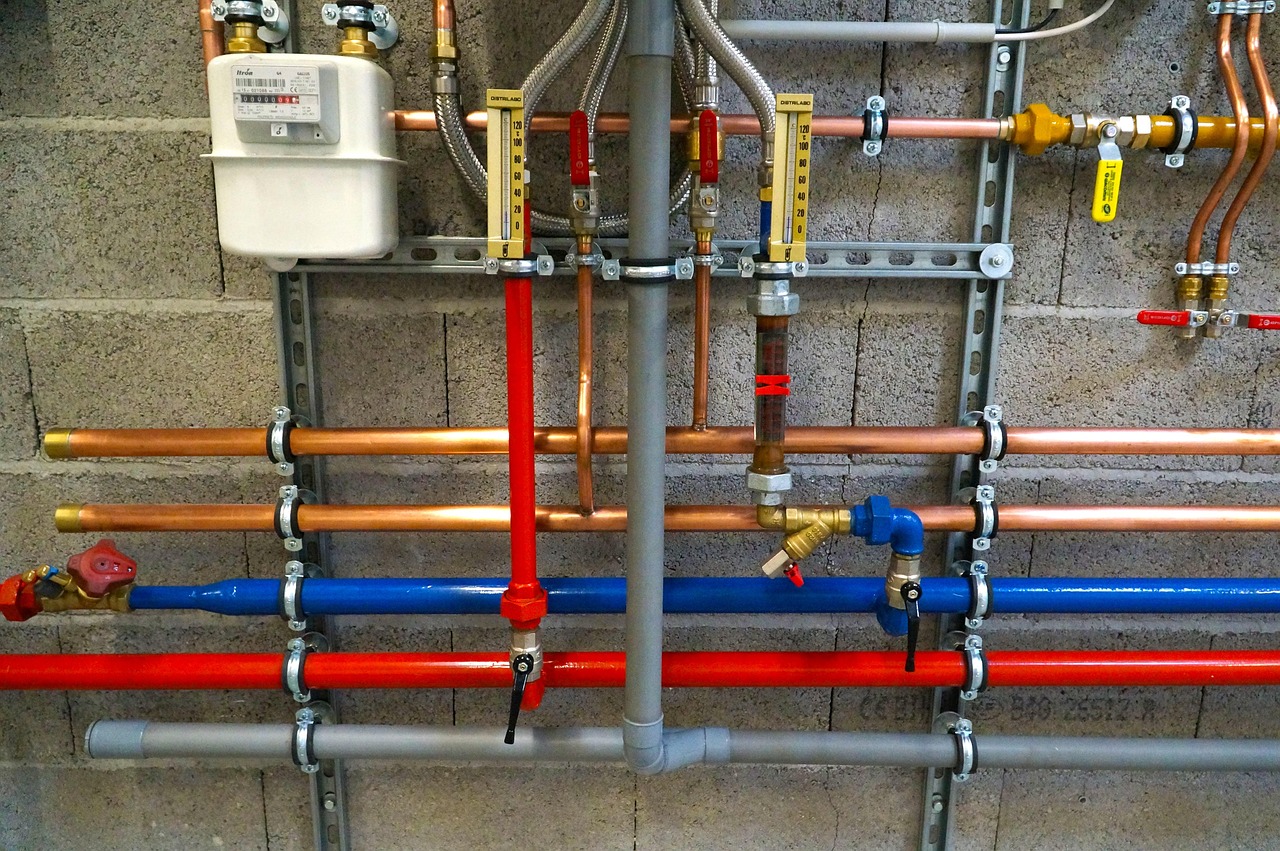
In Denver, with its unique water conditions, installing a water softener can be a game-changer for both your health and home. Denver water softener installation services offer a range of benefits that go beyond just improving the taste of your water. From enhancing personal hygiene to protecting your home’s plumbing, a well-installed water softener is…
Read More “The Benefits of a Water Softener for Health and Home in Denver” »